Risk
-
Theranos whistleblower on ‘metaphorical black box’ of AI
Speaking at the Radiance conference in Texas this week, Tyler Shultz urged attendees to create company cultures “where people are willing to speak up.”
By Dan Niepow • Feb. 25, 2026 -
Opinion
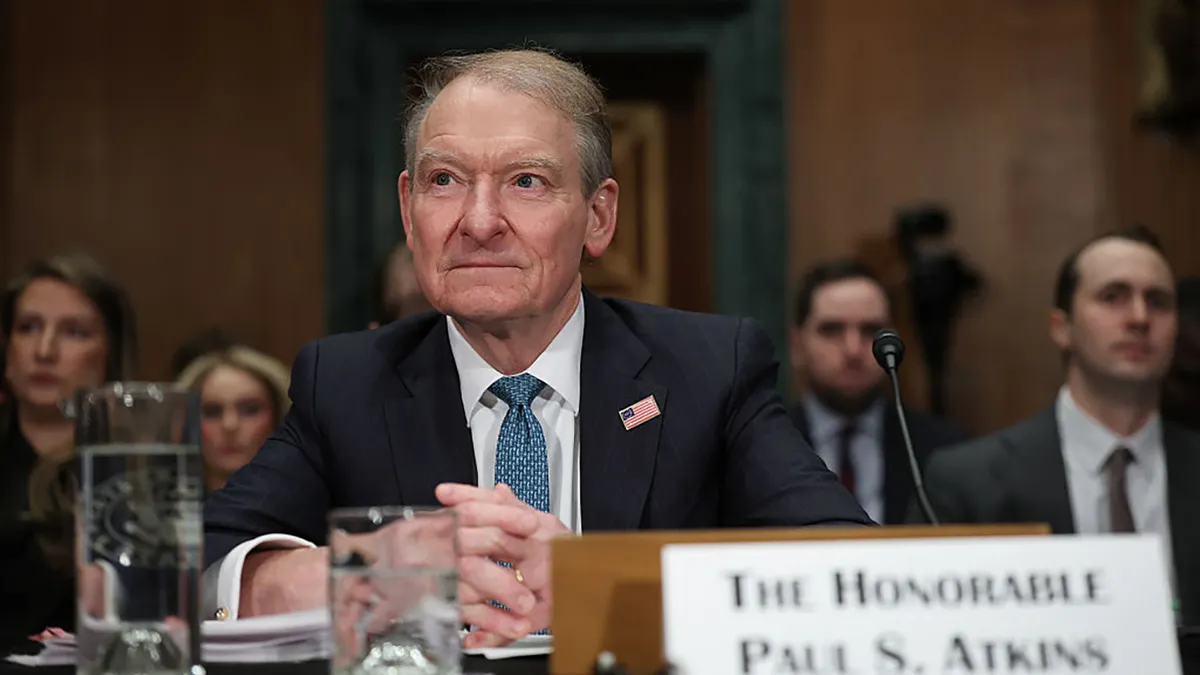
Is the SEC regulating for a pre-AI world?
The Securities and Exchange Commission’s outdated views on disclosures ignore technology and misattribute the decline in public companies to disclosure overload, writes CFA Institute’s Sandy Peters.
By Sandy Peters • Feb. 24, 2026 -
 Explore the Trendline➔
Explore the Trendline➔
 Getty Images
Getty Images Trendline
TrendlineTax policy shifts: What CFOs need to know to stay ahead
Discover how evolving tax policies are creating new opportunities and challenges for CFOs.
By CFO.com staff -
Ex-CFO’s lawsuit claims health care firm asked her to commit fraud
Rebeckah Hall, a 26-year employee of Mountain Comprehensive Care Center in Kentucky, said the company created a “hostile work environment” after she refused to engage in fraudulent billing practices.
By Dan Niepow • Feb. 20, 2026 -
Q&A
Protos Security CFO on the convergence of finance and operations
A longtime CFO-operator, Anthony Escamilla says that the two departments are "inseparable."
By Dan Niepow • Feb. 19, 2026 -
Jobs report resets rate outlook ahead of Fed leadership shift
From payroll revisions to Fed politics, January’s jobs report raises questions about the prospect of immediate rate cuts.
By Adam Zaki • Feb. 18, 2026 -
UCLA CFO blows whistle on university finances
Stephen Agostini halted reports, paused a costly ERP project and warned rising compensation and academic and athletics spending are driving a projected $425 million deficit.
By Adam Zaki • Updated Feb. 17, 2026 -
Florida media firm’s ex-CFO faces money laundering charges
Jeffery Crane was arrested in early February amid allegations he stole hundreds of thousands of dollars from his former employer.
By Dan Niepow • Feb. 17, 2026 -
Finance and sales teams don’t match up on criteria for deal approvals
Those on the more conservative finance side take a dim view of doing business with late payers.
By David McCann • Feb. 17, 2026 -
Opinion
What CFOs can do to close the cyber-ERM integration gap
Firms that connect cybersecurity with enterprise risk management gain a more complete view of risk. Here’s how finance leaders can foster a more unified approach.
By Kelley Pruetz and Kristen Senz • Feb. 10, 2026 -
Opinion
$8M for 30 seconds: A CFO’s guide to Super Bowl ad spend
Advertising around the Super Bowl can be worth it if you run it like a CFO. Not if you let the marketing team treat it like a trophy.
By Jason Hershman • Feb. 6, 2026 -
Florida CPA pleads guilty in federal fraud case
Prosecutors said Thomas Unsworth submitted false documents to the federal government to help others land emergency relief money.
By Dan Niepow • Feb. 3, 2026 -
Ex-Loretto Hospital CFO arrested in Serbia
A recent court filing says Anosh Ahmed, who left the U.S. amid fraud charges, was arrested in the eastern European country in late 2025.
By Dan Niepow • Jan. 30, 2026 -
Online sneaker seller’s CFO gets prison time for bank fraud conspiracy
Bethany Mockerman, who served as finance chief of collectible shoe seller Zadeh Kicks, concocted a “sophisticated, comprehensive scheme” to deceive banks into providing loans, federal prosecutors said.
By Dan Niepow • Jan. 29, 2026 -
ADM’s ex-CFO faces federal fraud charges
In court filings, the SEC says that Vikram Luthar, the ag giant’s former finance chief, misled investors by making retroactive “adjustments” to the performance of a key business unit.
By Dan Niepow • Jan. 28, 2026 -
Average enterprise business handles 40-plus bank accounts
A survey of finance leaders by fintech provider Adyen and Boston Consulting Group aims to quantify the complexities of running a large business.
By Dan Niepow • Jan. 28, 2026 -
Opinion
The CFO automation imperative: Balancing tech and human judgment
Finance leaders must embrace automation while safeguarding human judgment in financial decisions.
By Diana Mugambi • Jan. 27, 2026 -
44% of CFOs expect to benefit from One Big Beautiful Bill Act’s tax benefits
Anticipated savings are helping to create renewed interest in strategic spending, although concerns over the law remain.
By David McCann • Jan. 26, 2026 -
U.S. workers brace for displacement by AI
More than half worry about being laid off as soon as this year.
By David McCann • Jan. 23, 2026 -
Almost half of the time saved using AI is spent correcting outputs
Inconsistent outputs from large language models are introducing hours of additional labor for workers.
By Dan Niepow • Jan. 21, 2026 -
Companies expect to double their AI spending in 2026
Tellingly, CEOs are suddenly the key decision-makers on artificial intelligence, a big shift from a year ago.
By David McCann • Jan. 20, 2026 -
Economic fears prompt Americans to pare back on retirement savings
A new survey from Allianz Life shows a notable dip in the percentage of respondents who are still saving for retirement.
By Dan Niepow • Jan. 14, 2026 -
Opinion
Antitrust enforcers sharpen their focus on earnings calls
A new regime of closer scrutiny by the European Commission may influence U.S. regulators and courts.
By Parker Miller, Jens-Olrik Murach and Robert Poole • Jan. 13, 2026 -
Consumers head into 2026 with worries about inflation and jobs
A recent survey by the New York Federal Reserve points to persistent concerns about price increases over the year ahead.
By Dan Niepow • Jan. 13, 2026 -
SEC drops fraud case against mining CFO
The commission said it has agreed to dismiss the 2017 civil case against Rio Tinto’s former CFO Guy Elliott.
By Dan Niepow • Jan. 12, 2026 -
SMBs still fret about the economy but see good times ahead for themselves
After surviving a topsy-turvy 2025, companies are ramping up their growth plans.
By David McCann • Jan. 8, 2026